eCommerce servers are currently being specific with distant accessibility malware that hides on Nginx servers in a way that will make it pretty much invisible to safety answers.
The danger gained the title NginRAT, a blend of the application it targets and the distant access capabilities it supplies and is staying applied in server-facet assaults to steal payment card details from on line merchants.
NginRAT was observed on eCommerce servers in North America and Europe that experienced been infected with CronRAT, a distant access trojan (RAT) that hides payloads in responsibilities scheduled to execute on an invalid working day of the calendar.
NginRAT has infected servers in the U.S., Germany, and France exactly where it injects into Nginx procedures that are indistinguishable from reputable ones, making it possible for it to continue being undetected.
RATs allow server-aspect code modification
Scientists at safety enterprise Sansec make clear that the new malware is sent CronRAT, while both of them satisfy the same perform: giving distant accessibility to the compromised technique.
Willem de Groot, director of menace investigation at Sansec, instructed BleepingComputer that when making use of pretty different strategies to sustain their stealth, the two RATs seem to have the same position, performing as a backup for preserving distant accessibility.
Whoever is at the rear of these strains of malware, is using them to modify server-side code that permitted them to record info submitted by consumers (Submit requests).
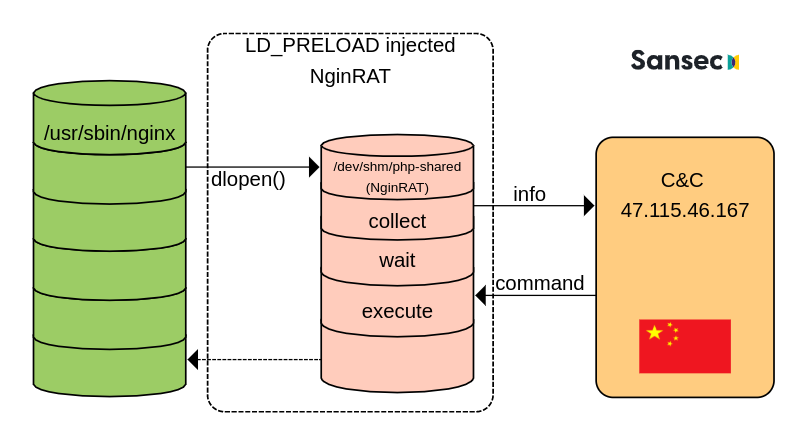
Sansec was in a position to study NginRAT just after creating a tailor made CronRAT and observing the exchanges with the command and control server (C2) positioned in China.
The researchers tricked the C2 into sending and executing a rogue shared library payload, as aspect of the typical destructive conversation, disguising the NginRAT “more advanced piece of malware.”
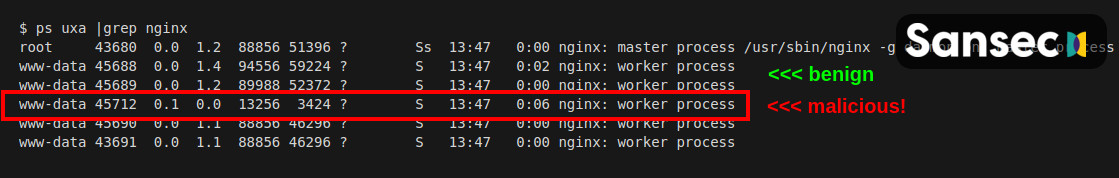
“NginRAT primarily hijacks a host Nginx software to stay undetected. To do that, NginRAT modifies main features of the Linux host method. When the legitimate Nginx internet server takes advantage of this sort of functionality (eg dlopen), NginRAT intercepts it to inject itself” – Sansec
At the conclusion of the course of action, the Nginx procedure embeds the distant accessibility malware in a way that helps make it almost unattainable to explain to aside from a reputable approach.
In a technological report right now, Sansec clarifies that NginRAT lands on a compromised program with the aid of CronRAT by way of the tailor made “dwn” command that downloads the malicious Linux technique library to the “/dev/shm/php-shared” site.
The library is then introduced making use of the LD_PRELOAD debugging element in Linux that is ordinarily employed to exam technique libraries.
Likely to mask the execution, the threat actor also additional the “help” option several situations at the conclude. Executing the command injects the NginRAT into the host Nginx app.
Mainly because NginRAT hides as a typical Nginx process and the code exists only in the server’s memory, detecting it may possibly be a problem.
Nonetheless, the malware is released applying two variables, LD_PRELOAD and LD_L1BRARY_Path. Administrators can use the latter, which includes the “typo,” to expose the energetic destructive procedures by functioning the subsequent command:
$ sudo grep -al LD_L1BRARY_Route /proc/*/approximativement | grep -v self/
/proc/17199/environ
/proc/25074/approximativementSansec notes that if NginRAT is discovered on the server, directors should really also look at the cron tasks due to the fact it is extremely probable that malware is hiding there, way too, included by CronRAT.





More Stories
What Are The Types of Magento Hosting Services
User Experience (Ux) Design Strategies For E-Commerce Sites
TikTok is wading into South-East Asia’s e-commerce wars